Building Secure Mobile Apps: Essential Strategies for App Security
Security always needs to be a top-of-mind concern for businesses. This is especially true for companies with mobile apps.
A data breach or hack can cause significant damage to your organization. Security breaches are not only expensive, but they can also crush your reputation.
To ensure security for your business and customers, you must take app security seriously.
That’s why I created this guide. First, I’ll explain some common mobile security flaws and vulnerabilities for mobile devices. Then I’ll show you how to build secure mobile apps.
Key Takeaways
- Importance of App Security: Mobile app security is crucial to protect both business and customer data.
- Common Threats: Be aware of data leakage, malware, and compromised passwords as major security threats.
- Platform Vulnerabilities: Android devices are more susceptible to malware due to third-party app stores.
- Update Necessity: Keeping software and operating systems updated is vital for security.
- Encryption Needs: End-to-end encryption is essential for protecting data in transit.
Mobile App Security Threats
Most businesses understand the importance of securing websites, databases, and cloud storage systems. But mobile app security is just as important, if not more important than these other categories.
Think about the scale of your mobile deployment. It might be installed on tens of thousands of mobile devices—maybe more.
Mobile app security issues are more prominent than you might realize. In fact, 70% of all internet fraud can be traced to mobile devices. One in five hacks come from rogue mobile apps, and there’s a high-risk mobile app installed on one in 36 mobile devices.
Let’s talk about some common application security threats and mobile app security vulnerabilities you need to be aware of.
Data Leakage
According to a recent study, 85% of mobile apps have little to no security protection. Hackers and cybercriminals have realized this and have increased the frequency in which they target mobile infrastructures.
When a user downloads an app, they generally grant the app certain permissions to other data on the device. So if a hacker can penetrate the app, they’ll gain access to sensitive data beyond the primary use-case of the app.
This could include digital wallets and passwords. If it’s an internal app for employees, the hackers can get their hands on sensitive corporate data as well.
Malware and Spyware
Like computers, mobile apps are also susceptible to malware.
Some devices are more susceptible to malware threats than others. In fact, a new study found that Android devices are 47 times more likely to carry malware than Apple devices.
| Aspect | Android | Apple |
|---|---|---|
| Malware Susceptibility | 47 times more likely | Less likely |
| App Store Policy | Supports third-party stores | Restricts to official store |
That’s because Androids support third-party app stores more than iOS. It’s easier for an Android user to download apps from somewhere other than the Google Play Store.
Nearly one in four people think it’s safe to download third-party mobile apps as long as those apps aren’t accessing corporate data.

This is something that Android developers really need to be aware of. Once a malicious app has been installed on a user’s device, it could compromise the other apps on their device as well—even the ones downloaded from legitimate sources.
Compromised Passwords
Our society has a huge problem with passwords right now. Since so many different tools, accounts, and subscriptions require a password, people just reuse the same passwords across multiple accounts.
So if one account is compromised, hackers can run wild across other accounts as well.
What would happen if one of your developers or someone on your software development team had a compromised password? Could a hacker use that password to gain app access on the backend of your software?
If yes, that poses a huge risk to your organizational data and app users. Cybercriminals could use that access to deploy malicious links or hacks directly to all users who have your app installed.
Outdated Operating Systems and Software
Failing to keep all of your devices, software, and OS up to date is a mobile security vulnerability.
As malware, ransomware, and other cyber attacks become more advanced, outdated software can’t detect and prevent newer attacks. But many software updates contain security patches. This holds true for mobile apps, mobile devices, and mobile security as well.
Check out these graphs Verizon’s Mobile Security Index Report:
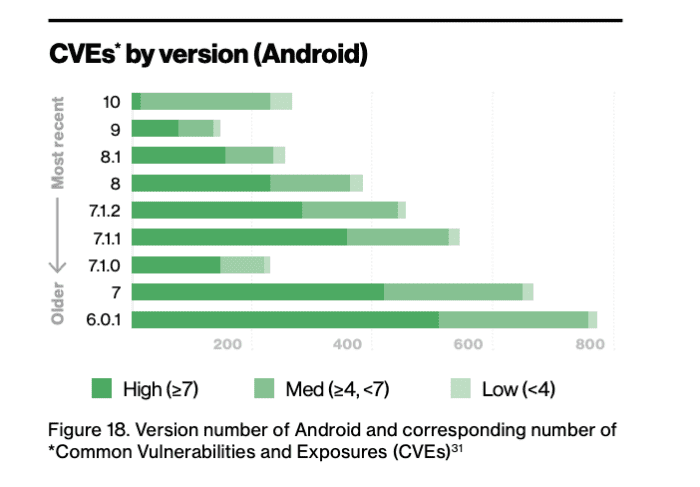
As you can see, newer Android versions contain fewer CVEs (common vulnerabilities and exposures).Just a fraction of the newest Android releases contain high security vulnerabilities.
Now let’s look at Apple’s CVE’s by iOS version:
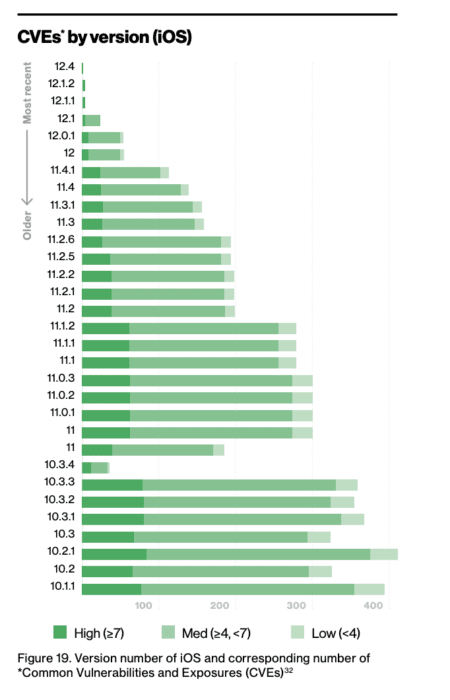
It’s safe to say that this graph speaks for itself.
If people are using mobile devices that haven’t been updated to the latest OS, they’re significantly more susceptible to mobile security threats.
Social Engineering and Phishing
Social engineering is on the rise for mobile. Also known as phishing, this occurs when hackers send fake emails, text messages, or malicious ads in an effort to access passwords or private information.
We’ve all seen these before. You get an email from someone claiming to be Apple or another reputable business, telling you to reset your password or update an expired credit card.
Shockingly, nearly 60% of people say they can’t confidently identify social engineering attacks. Roughly 40% think it’s smart to reply to these attacks.
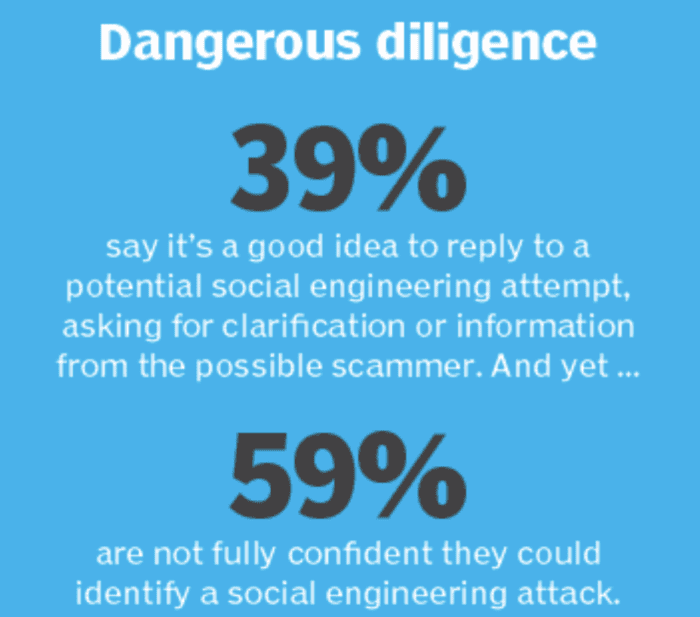
These numbers are alarming and pose a threat to mobile applications and developers.
Encryption Gaps
End-
Frequently Asked Questions
How can I protect my mobile app from data leakage?
To protect your mobile app from data leakage, ensure that you implement strong encryption protocols and limit app permissions. Platforms like Buildfire make this straightforward by offering built-in security features.
What are the best practices for preventing malware in mobile apps?
Preventing malware involves regularly updating your app and using secure coding practices. Buildfire, for instance, offers tools to help developers maintain app security through regular updates and patches.
How do I secure my app against compromised passwords?
Implementing multi-factor authentication and educating users about strong password practices can help secure your app. Tools like Buildfire allow businesses to integrate these security measures easily.
Why is it important to keep mobile operating systems updated?
Keeping mobile operating systems updated is crucial because updates often contain security patches that protect against new threats. Outdated systems are more vulnerable to attacks.
What steps can I take to prevent social engineering attacks on my app?
Educating users about recognizing phishing attempts and implementing security features like two-factor authentication can help prevent social engineering attacks.
If you decide to code an app on your own, that’s fine too. Handling the security aspects will be a bit more of a daunting task. But your life will be easier if you follow the tips and best practices explained in this guide.
Frequently Asked Questions
- What is end-to-end encryption?
- End-to-end encryption is a method of data protection where only the communicating users can read the messages.
- Why is mobile app security important?
- Mobile app security is crucial to protect user data and prevent unauthorized access to sensitive information.
- What are some common security vulnerabilities in mobile apps?
- Common vulnerabilities include insecure data storage, weak server-side controls, and insufficient transport layer protection.
- How can I secure my mobile app?
- Implementing encryption, using secure authentication methods, and regularly updating the app can help secure it.
- What is a no-code app builder?
- A no-code app builder is a platform that allows users to create apps without writing code, often with built-in security features.